News
VS Code Goes on Security 'MITRE ATT&CK' with New Extension
Security firm Red Canary has open sourced a new Visual Studio Code extension that helps security analysts and engineers interact with the MITRE ATT&CK framework with the help of editor features like code completion, hover pop-ups and searching of attack techniques.
The eight-year-old MITRE ATT&CK framework was created by security company MITRE to provide a free, globally accessible, curated knowledge base and model of cyber adversary tactics and techniques based on real-world observations. The name stands for "MITRE Adversarial Tactics, Techniques, and Common Knowledge." The framework is used by organizations of all types to improve security by better understanding attacker models, methodologies and mitigation.
For example, the Enterprise Matrix (shown below) includes information for Windows, macOS, Linux, PRE, AWS, GCP, Azure, Azure AD, Office 365, SaaS and Network. The matrix lists various techniques under headings such as Reconnaissance, Initial Access, Credential Access and more. Techniques for Reconnaissance include Active Scanning, Phishing for Information and so on. Drilling down further, an Active Scanning sub-technique is listed as: "Before compromising a victim, adversaries may execute active reconnaissance scans to gather information that can be used during targeting. Active scans are those where the adversary probes victim infrastructure via network traffic, as opposed to other forms of reconnaissance that do not involve direct interaction." It then provides mitigation and detection information.
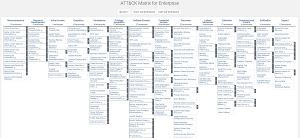 [Click on image for larger view.] MITRE ATT&CK Enterprise Matrix (source: MITRE ATT&CK ).
[Click on image for larger view.] MITRE ATT&CK Enterprise Matrix (source: MITRE ATT&CK ).
With the new open source MITRE ATT&CK for Visual Studio Code tool that's available from the VS Code Marketplace, drilling down into data like that is easier, allowing for interaction with the framework from within the editor using common coding techniques including:
-
Code Completion: This extension provides IntelliSense-like support for ATT&CK tactics, techniques and sub-techniques. This includes completions for technique names too, so typing either
Powers or T1059.001 will insert the appropriate text.
If enabled, code completion is supported for Group, Mitigation, and Software IDs/names. However, by default, these providers are disabled. To enable them, go into the vscode-attack section of Settings and check which objects you would like to enable.
-
Hover: This extension provides descriptions when hovering over tactic and technique IDs, which include the name, MITRE ATT&CK source link, and configurable descriptions pulled from the ATT&CK technique information.
Like code completion, hovers are supported for Group, Mitigation, and Software IDs, and they can be enabled using the appropriate toggles.
-
Technique Search: This extension provides a command that allows searching for techniques by their technique IDs, names, or interesting keywords found in the descriptions.
For example, searching for the keyword certutil, which is not present in any technique name, will yield a result for T1140 Deobfuscate/Decode Files or Information, because there is a reference to it in the description. Any matching techniques reveal webpanel with results similar to those found in the hover results.
 [Click on image for larger, animated GIF view.] MITRE ATT&CK Tool in Animated Action (source: Red Canary).
[Click on image for larger, animated GIF view.] MITRE ATT&CK Tool in Animated Action (source: Red Canary).
"Many of our internal teams map their work to the ATT&CK framework," said an April 14 blog post from Red Canary, which sells a security platform specializing in Managed Detection & Recovery and other techniques. "For example, our detection engineering team maintains a living library of thousands of behavioral detection analytics that we associate with corresponding ATT&CK techniques or sub-techniques whenever possible. Similarly, our threat intelligence team uses ATT&CK tactics and techniques to help organize and standardize the threat profiles they produce to inform the CIRT, our customers, and the broader information security community.
"These teams needed a way to search, identify, and integrate ATT&CK directly into their development processes, and since many of them already used Visual Studio Code, creating this extension was a natural fit. This has the added benefit of allowing us to easily customize how we integrate ATT&CK on a per-project basis. Often, our detection engineers will only reference ATT&CK techniques by their ID, while our threat intelligence team will use the entire technique name, including sub-techniques. We've baked this customization into the extension, so even if you wear multiple hats in your organization, this tool will fit your diverse needs."
While the tool was developed to address the firm's admittedly narrow internal needs, Red Canary has a list of features it would like to add, which now could come via community contributions as well as from its own developers.
"We certainly hope that members of the infosec and ATT&CK community both find this tool useful and contribute new features that satisfy their own use cases," Red Canary said.
As of this writing, the two-week-old tool has been installed 329 times, with 8 stars awarded to the open source project.
About the Author
David Ramel is an editor and writer at Converge 360.